If we want to talk about companies specializing in telecommunication tools and other technology products, we will name Cisco in the top 5 companies in the world, due to its privileged position.
Cisco is one of the largest companies in the world in the field of security, network, collaboration, cloud management, and more solutions that help connect secure industries and communities.
The name of Cisco is taken from the word “San Francisco”, where the famous “Golden Gate Bridge” is located. Cisco uses the largest technology and a deep understanding of the pattern of the network economy. These features make it one of the most successful applications and network operators. Cisco also provides large courses and applications for training and various certifications such as cyberspace, Python programming, networking, the Internet of things (IOTA), and data.
At the same time, Cisco is committed to playing a role for many companies as a “massive communications interface.” this feature of deep insight into the rich experience of industry and advanced technology has been experienced over the years, and these capabilities have been used to help companies transform network applications into strategic assets, fully use the potential and energy of the network and search for discovering competitive advantages in this field.
Here are some examples of Cisco’s performances:
- Network Slice Selection Function (NSSF)
- Network Responsibility Function (NRF)
- Policy Control Function (PCF)
- Session Management Performance (SMF)
- User Plane function (UPF)
- Provide a common NFV-compliant platform for Cisco mobile core functions
- To connect layer technologies such as LAN, WAN Wireless, and wired network
- To provide an internetwork operating system (IOS) that controls and manages the hardware on which it runs and from routing Switches and features3 support networking
- To secure network resources and control unauthorized access using various tools and protocols
- To provide scalability for ease of network growth and keep the network steady using cloud-native principles and technology
Company History

Cisco initially intended to name its company “San Francisco,” but, because of limitations in U.S. law that no company has the right to use the city name for its company, Cisco decided to sign the last five letters of San Francisco, Cisco of course, For its LOGO used the famous bridge of the city, “the Golden Gate Bridge”, which over time changed it and became modern.
Cisco Systems, Inc. was founded in December 1984 by a couple at Stanford University in the United States: Mr. Leonard Bosack, director of the computer center in the Department of Computing, and Mrs. Sandy Lerner, the director of the computer center at the Faculty of Commerce. he also designed a network-based device called “Router multiple Protocols.” the invention was used on the campus’s network Stanford made a United one. This connected device is a sign of the actual arrival of the connected era. In 1991, John Chambers joined Cisco took over the government, and transformed Cisco into a generational dynasty.
Cisco products and services

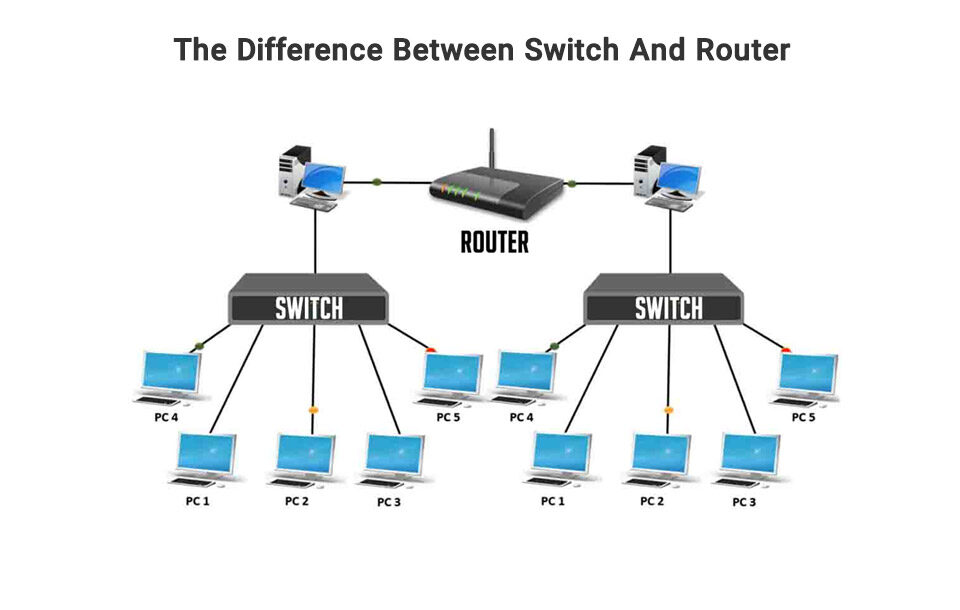
routers
Cisco-built routers, switches, and other devices manage about 80% of the world’s Internet communications. Over the past 20 years, Cisco has become the legend of the new economy in Silicon Valley. Cisco is rhymed All around the world with the words “Internet, productivity, Web applications” and has become a market leader in every area it enters.
Cisco operating system
Cisco’s network equipment, which is very diverse, from routers to suites and terminals, often requires a dedicated operating system to work. Cisco has also launched its exclusive operating system for users’ convenience, which is used for network products.
The operating system inside the network, “Internetwork operation System”, which is called IOS, is a family of dedicated network operating systems built and delivered in several Cisco router models and network switches.
This operating system is a set of telecommunication functions, routing, Internet operations, and switching that are integrated into a multi-function operating system. Although the IOS code base has only one common core, most IOS features can be used for use in Cisco products to other cores, such as Linux and QNX.
Unfortunately, all network products do not support the Cisco IOS. An example of these exceptions is the Cisco Catalyst switches that support the IOS XE and IOS-XR operating systems. The two operating systems mentioned are both Linux.
In data center environments, Cisco Nexus (Ethernet) Ethernet switches and Cisco MDS (Fibre) Channel both support the NX-OS operating system, which is based on Linux.
The limitation of hardware resources for routers and switches in the decade 1980 led to the formation of a Cisco ISO integrated architecture, meaning that all processes have direct hardware access to CPU processing.
There is no memory protective mechanism between processes, and the IOS continues with a specific timing from the run-up to completion, which does not prevent the core from continuing the running process.
Instead, before other processes have the opportunity to run, the process being implemented must communicate with the core and, if done, the next step will be implemented.
Cisco recommends that all Cisco IOS devices implement the authentication, licensing, and approval security model (AAA).
This protocol can use “TACACS”, “radius”, as well as local databases. The priority is with the first two protocols, and local databases are usually for emergencies.
Network Emergency Response System

This technology, which is based on Cisco employees during natural disasters and other public crises at the desired location, is known as one of their newest technologies for use in critical situations, network emergency response technology (NERV).
Wired and wireless services, including voice and radio calls, voice calls via IP, which is briefly VOIP Network-based video monitoring, and high-quality and secure video conferencing at a maximum speed of 3 to 72 Mbps. All of these technologies are based on cars.
A 1.8-meter satellite antenna provides the task of providing the bandwidth needed to communicate through this technology.
NERV is based on Cisco’s central sites in California and at the Triangle, North Carolina Research Park, and provides strategic deployment in North America. They can be fully operational within 15 minutes after the crisis
NERV was used for events such as the California fire in October 2007.
High-capacity diesel fuel tanks allow the largest vehicles to operate continuously for up to 72 hours.
Katrina, Gustav, Aik, San Bruno gas pipeline blast in 2010 and Sandy storm in 2012 were used by the Cisco Emergency Response System.
Cisco has maintained and deployed smaller and more responsive communication kits for emergencies outside North America by its crisis management team. Examples of the team include earthquakes in Haiti and New Zealand.
In 2011, the technology was also used for Brazilian flood victims as well as the 2011 earthquake and tsunami in Japan
Software Products
Cisco Tenentcom: An add-on for RTX Tenentcom. This solution integrates Cisco and Tencent for the corporate communications interface RTX Tencent Messenger and Cisco. For this reason, users of the original RTX messenger remained unchanged. Through Cisco Tencent, users can review their audience status, make high-quality HD voice-in and video calls, participate in online meetings or video conferences, and more…
Firewall
With employees, up-to-date data, and offices across this area, your firewall should be ready for anything. A secure firewall helps you plan more precisely, prioritize better, and close the system’s gaps to prevent disaster as best as possible
Network switch
Network switches in the platform are divided into three categories:
Access switches
- These switches consider the business and optimize it as best as possible.
Distribution switches and core
- Finding and understanding the network’s performance will achieve and provide reliable solutions.
Data center switches
- infrastructure growth and development provide flexibility and durability of the service with the help of designing and building the center’s network.
Cisco training

The “CCNA” course is required to enter the Cisco market, and you must first spend it on the level of routing and switching, which is referred to as the S&R level.
If you’ve searched for Cisco courses, you’ve heard the names of Entry, associate, professional Expert, and Architect.
These phrases represent the Cisco courses and documents level, which we will explain below.
“CCENT course”
The CCENT course level is for entry, which is also known as “ICND1”.
In this course, the understanding of network layers is from 1 to 3, which is usually related to routing and switching training.
People who participate in this course get acquainted with the advanced technologies and this field is an important point to begin their success in many of the networking jobs. This pre-course is required for the “CCNA” course.
“CCNA & CCDA Courses
After completing the Entry level, you will enter the associate level. To complete this level, you need to complete the CCNA and CCDA courses. You will learn how to install and configure Cisco switches and routers as well as wireless controllers during this period.
Another thing you’ll learn will be how to manage your network equipment and increase security, and learn how to do it with network programming.
CCNP & CCDP Courses
Another level you need to step on is the professional part. The prerequisite for this level is that you have to complete CCNP and CCDP courses. The purpose of this course is to get acquainted with skills such as managing and troubleshooting large networks that are mainly based on routing and routing topics.
You will also be taught tutorials on wireless and local network security service quality and SDN.
CCIE & CCDE Courses
EXPERT is the highest degree in Cisco education, with few people able to achieve this degree, CCIE and CCDE.
CCAr Course
The people who spend this course will reach the level of Architecture, which is the last level of the Cisco courses.
Company’s Awards
- Military Friendly Employer: ranked 2nd in the U.S. as a Military Friendly Employer
- 1st US Best Workplaces: Ranked 1st Best Workplace in the U.S. two years in a row!
- 3rd World’s Best Workplaces
- Ranked one of the World’s Best Workplaces twelve years in a row!
- In 2023, Best Places to Work in the U.S. by Glassdoor, six years in a row!
- In 2022, 3rd Best Large Workplaces for Women in the U.S. by “Fortune”
- …
Related businesses with the CCNA certification
Technical support expert
Helping and technical support to customers and employees of the company to solve the technical issues of computer devices in the fastest and easiest way possible. Technical backups communicate with customers through telephone calls, online chats, etc., or explain how employees work with devices.
Network management
Proper network management should do the following:
monitoring the networks of a company, managing updates, training employees about proper network maintenance and operation, troubleshooting existing problems, optimizing the network, providing up-to-date solutions, and maintaining, and checking the security of organization networks that are of great importance.
IT Security specialists
Those who act as IT security specialists should always check the computer systems of a company in terms of security and possible damage.
These professionals should be able to choose appropriate and up-to-date protection tools and use tools that identify malware and provide the necessary measures against cybersecurity threats.
Another task of these professionals is to improve the security of the network that encrypts emails and communications between companies and customers, promote systems, and design a firewall. ultimately, they limit access to confidential data stored on computers, networks, and servers.
VoIP Engineer
A VoIP engineer is the one who is responsible for installing and maintaining VoIP systems for organizations. His expertise is in configuring internal telephone systems, enhancing the security of all hardware and accessories, and to support all organization needs, and installing software in the organization.
Wireless Engineer
The activity of the wireless engineer is generally checking the Internet connection. Setting up and managing it, and maintaining and updating network equipment are one of the tasks that wireless engineers have to do.
It is also up to wireless engineers to troubleshoot Internet problems, manage firewalls, licenses, and test the proper functioning of networks and routers.
Network Security Engineer
An organization and company need to design and manage network security systems, this is the responsibility of security engineers.
Optimizing systems, applying training for users, checking network protocols, and developing and upgrading the system to improve the performance of network security engineers.
But the most important task of network security engineers is to protect against security damage such as malware, hackers